Try the world's most popular OSINT platform for free. Elevate your enterprise investigations with unmatched accuracy.
Jordan investigated 342 Russian embassy emails with OSINT Industries. This is what he found.
"I thought it would be easier to carry just one device for my work and for my personal emails instead of two… and obviously, it hasn't worked out that way.” – Hillary Clinton, [Source: BBC]
By now, an email scandal is almost an electoral tradition. American politics and high-profile email controversies go together like bread and butter - or peanut butter and jelly, to be more accurate.

Email has been at the centre of some of the most consequential political revelations of this century, and that’s excluding the legend of ‘Hillary’s emails’. To start that year, an internal audit by the U.S. Inspector General found Ambassador Caroline Kennedy and other senior staff at Tokyo’s US embassy used personal email accounts for official government business, including messages classified as “sensitive but unclassified (SBU).” By midway through 2016, the Democratic National Committee (DNC) - central organisational body for the U.S. Democratic Party - saw Russia-linked hackers Guccifer 2.0 get their hands on 19,000 emails and 8,000 attachments from senior figures. With primary campaigns ongoing, DNC chair Debbie Wasserman Schultz could have done without exposure of party bias against then-candidate Bernie Sanders. Wasserman Schultz was prompted to resign shortly before the party convention, and the lesson she learned was pretty blunt: once your email security fails, you lose control over information forever.
Still, by March, campaign chair John Podesta had fallen victim to a spear-phishing email. An aide had made a typo, writing: “This is a legitimate email… John needs to change his password immediately.” The FBI and CIA assessed the same Russia-linked group was to blame.
"The sort of ways you handle personal mail and the way you handle highly sensitive mail is very different… This is why security-conscious enterprises want to keep a complete separation.” – Nicko van Someren, CTO for secure communications company Good Technology Corp. [Source: USA Today]
Republican Colin Powell, former U.S. Secretary of State under President George W. Bush conducted official government business using a personal AOL email account for over twenty years. When Powell’s personal AOL account was another victim of 2016, a cache of his emails exposed a shocking amount of foreign policy, internal political dynamics, and unfavorable assessments of other officials. He’d even offered advice to other officials on managing government correspondence outside official systems - and around 90 had taken up the challenge.

Hillary Clinton, John Podesta, Colin Powell, Caroline Kennedy, Jared Kushner, Steven Miller, Mike Pence, Reince Priebus, Sarah Palin, National Security Adviser Michael Waltz, Obama’s transition team and Ivanka Trump have something in common. They all failed to learn lessons about bad email security.
Using a Blackberry, AOL, Gmail or some other platform, they have all used private emails for government business or government emails for private business. Many of these figures have suffered far-reaching consequences, and not just in the court of public opinion. The post-2016 compromise and public release of political and embassy emails in the United States demonstrates above all else that dangerous email behaviors will be weaponised for geopolitical effect. The pattern with perpetrators exploiting these soft spots has made another world power just as synonymous in the news with email: Russia.
Global cybersecurity reporting indicates that Russia-aligned email attack campaigns have targets that extend even beyond politics. Data pillaged from vulnerable emails - crossover between personal and official accounts being a prime source of vulnerability - is invaluable to Kremlin-backed operators. Civil society organisations, NGOs, and even former ambassadors are easy targets for Russian bad actors seeking to harvest credentials or infiltrate sensitive networks - all because somebody made a poor choice about an old Hotmail account.
But does Russia have its own email vulnerabilities?
Back in October 2016, Ukrainian hacktivists CyberHunta proved they might. The collective, part of the wider Ukraine Cyber Alliance, did so to the tune of a 1GB dump including 2,337 emails. Vladislav Surkov, Russia’s ‘grey cardinal’ managing Russian policy toward Ukraine, let his assistants use a vulnerable inbox to send data and attachments related to separatist coordination, including correspondence with separatists like Denis Pushilin.

The Kremlin was quick to deny the authenticity of the leak. That the emails included scans of Surkov’s passport and family documents made this difficult to say the least. Since Surkov, we’ve seen the likes of the 2021 Vulkan Files and 2023 Cyber Resistance 11GB mail hack on Deputy Duma Chairman Aleksandr Babakov.
Now a new report shows an OSINT Industries-backed researcher proving Russian diplomats, when it comes to email, are stuck in 2016. They’re still making the massive email mistakes that good guys - or worse, even badder guys - can exploit. With just a little OSINT, a keen analyst would be able to turn the tables on Russian leakers; the fault for which would lie with embassies themselves.
There are approximately 143 Russian embassies worldwide, across every continent. This is what gets exposed when you search their public email addresses on OSINT Industries.
“In retrospect, as I look back at it now, even though it was allowed, I should have used two accounts. One for personal, one for work-related.” – Hillary Clinton, [Source: Guardian]
Meet Jordan, an OSINT/SOCMINT Analyst.
Jordan S. is an OSINT/SOCMINT Analyst, and an OSINT Industries user. A stellar example of an independent OSINT professional, Jordan’s investigations have been previously featured as Case Studies.
OSINT has supported Jordan’s work from video game writing to due diligence, SOCMINT, missing persons, and journalistic efforts - including in difficult OSINT climates like Japan. It’s been a part of Jordan’s life since he “was 11, without even knowing it”. Soon he was a teenager “tracking down sources of information for facts that had a [citation needed] template” on wikisites.
Jordan began his career as a Deputy Director. Now, his own site employs a Deputy Director under him. Constantly scouting for opportunities to put his OSINT analysis skills to the test, OSINT Industries is an everyday part of Jordan’s workflow.
This time, inspired by OSINT Industries CEO Nathaniel Fried’s Donetsk and South African government email investigations, Jordan looked Eastward.
“Much has been said about federal officials using personal email accounts to conduct government business and why that’s a bad idea, yet this still continues.” – Jordan, an OSINT and SOCMINT Analyst [Source: OSINT Industries]
Jordan found that Russia’s 143 embassies worldwide publicize official emails as points of contact: a disclosure that “opens up many new avenues for collection of OSINT”. Painstakingly, he collected on a spreadsheet 324 email addresses for every Russian embassy in the world, and began to use our platform to follow their digital footprints.
Running official addresses through OSINT Industries, it’s normal to expect few if any registrations to online platforms and consumer services. At least, that’s how it should be.
You’ve Got Mail, Moscow: The Scale of Exposure
“This is not a normal distribution of accounts for official Russian government email addresses…” – Jordan, an OSINT and SOCMINT Analyst [Source: OSINT Industries]
Running 324 official worldwide Russian embassy email addresses through OSINT Industries, Jordan found an astonishing number of hits:
Compared to other government examples, the number of signups was extremely anomalous. Jordan found that in addition to - “or instead of” - diplomatic communications, Russian diplomats are using their emails to sign up for Facebook, Call of Duty and XVideos. Dating service WayToHey and LovePlanet had one signup each.
Even worse, many of Russia’s diplomatic emails are flawed from the start: two email addresses are registered with Yahoo, two are registered with Hotmail, fifteen are registered with Gmail, one is registered with MSN, and eighteen are registered with Yandex. Personal email providers like these offer nothing near the level of security required for diplomatic communications.
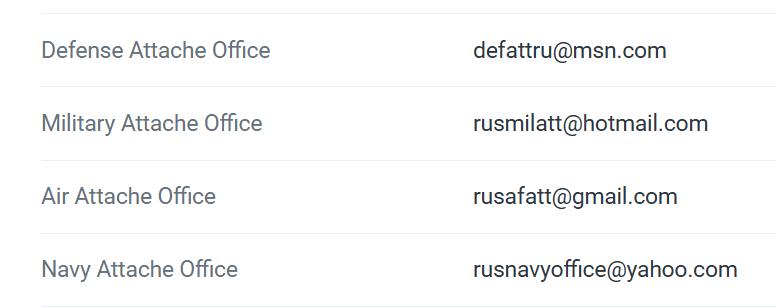
Russian attaché office contact email addresses. [Source: OSINT Industries/Jordan S. via washington.mid.ru)
Jordan then found the defense, military, air and navy attaché offices of the Russian embassy in Washington, D.C. don’t use secure email services either. They advertise their emails as defattru@msn[.]com, rusmilatt@hotmail[.]com, rusafatt@gmail[.]com and rusnavyoffice@yahoo[.]com respectively. The security risk this creates is incalculable.
“Personal email accounts… They are prime targets for attackers.” – Nabil Hannan, chief information security officer at NetSPI. [Source: WSJ]
OSINT Industries searches suggest separation of personal and private is being altogether ignored by Russian embassy officials; officials often occupying extremely sensitive positions in their host countries. Next, Jordan set out to investigate just what it is these accounts are up to. What, we might ask, does a Russian diplomat post on Instagram?
Signed Up and Signed Away: The Attack Surface Expands
Jordan delineated his findings by OSINT Industries module: Yandex, Facebook, Twitter, and Google. Even a routine digital presence on each platform leaves an open door for OSINT, and serious operational security risks for embassies.
Yandex (Яндекс)
31 of the email dresses used had accounts on Yandex, effectively Russia’s Google. More than just Russia’s dominant search engine, Yandex - like Google - is an email provider through Yandex Mail, a cloud storage platform, a maps site, a browser, a way to hail rides and most recently an AI provider.
All but 2 of the Yandex accounts use the Russian coat of arms as their profile picture. Two don’t. The first, rusconsbasrah-iraq@yandex[.]ru or username “Vagif G.” and a profile picture showing an unknown building. The second, rusemb-minsk@yandex[.]rugoes a step further. It shows the Russian embassy in Minsk, Belarus. Bad actors could potentially geolocate the building from this image with relative ease.
Reports suggest the Surkov leaks occurred in part through Yandex-linked inboxes.
Facebook and Twitter
46 embassy emails are connected to Facebook accounts.
If this wasn’t already inappropriate enough, using OSINT Industries on the Tokyo embassy email (pressjp@mid[.]ru) reveals a hint for an additional email address via Facebook: t*****1@gmail[.]com. The Zimbabwe embassy email russconswdc@gmail[.]com reveals a second partial email via Facebook too: r*****c@y*******[.]ru. The same occurs with veleposlanstvo-ruske-federacije@zg[.]htnet[.]hr, the address for Russia’s Croatia embassy in Zagreb: OSINT Industries’ Facebook module reveals v*****e@y*******[.]ru.
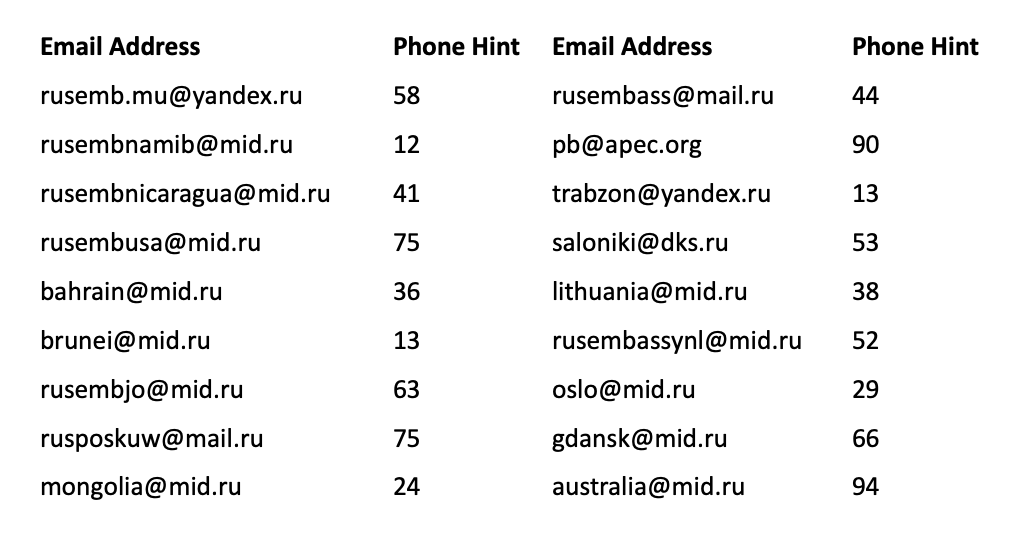
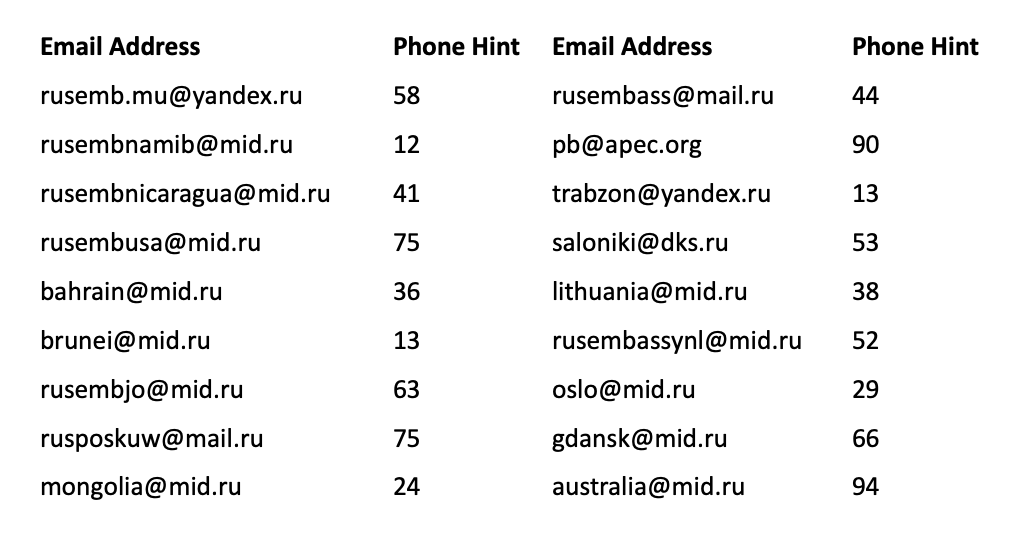
Jordan found 20 of the Facebook accounts have additional phone number hints:

These include at-risk states like Pakistan, Iran and Norway. By linking embassy emails to Facebook accounts, these diplomats take the risk of bad actors (or competent analysts) finding these personal emails and phone numbers, likely added as credential-recovery data. Phishing, SIM-swap attacks, and account takeover become a whole lot easier with this data accessible through simple OSINT - no advanced hacking required.
Likewise, 72 Russian embassy email addresses are registered on Twitter. OSINT Industries identified 18 that have partial phone number hints, including states as major as Australia:
Google Maps
Every OSINT investigator or analyst knows Google Maps is crucial for GeoINT.
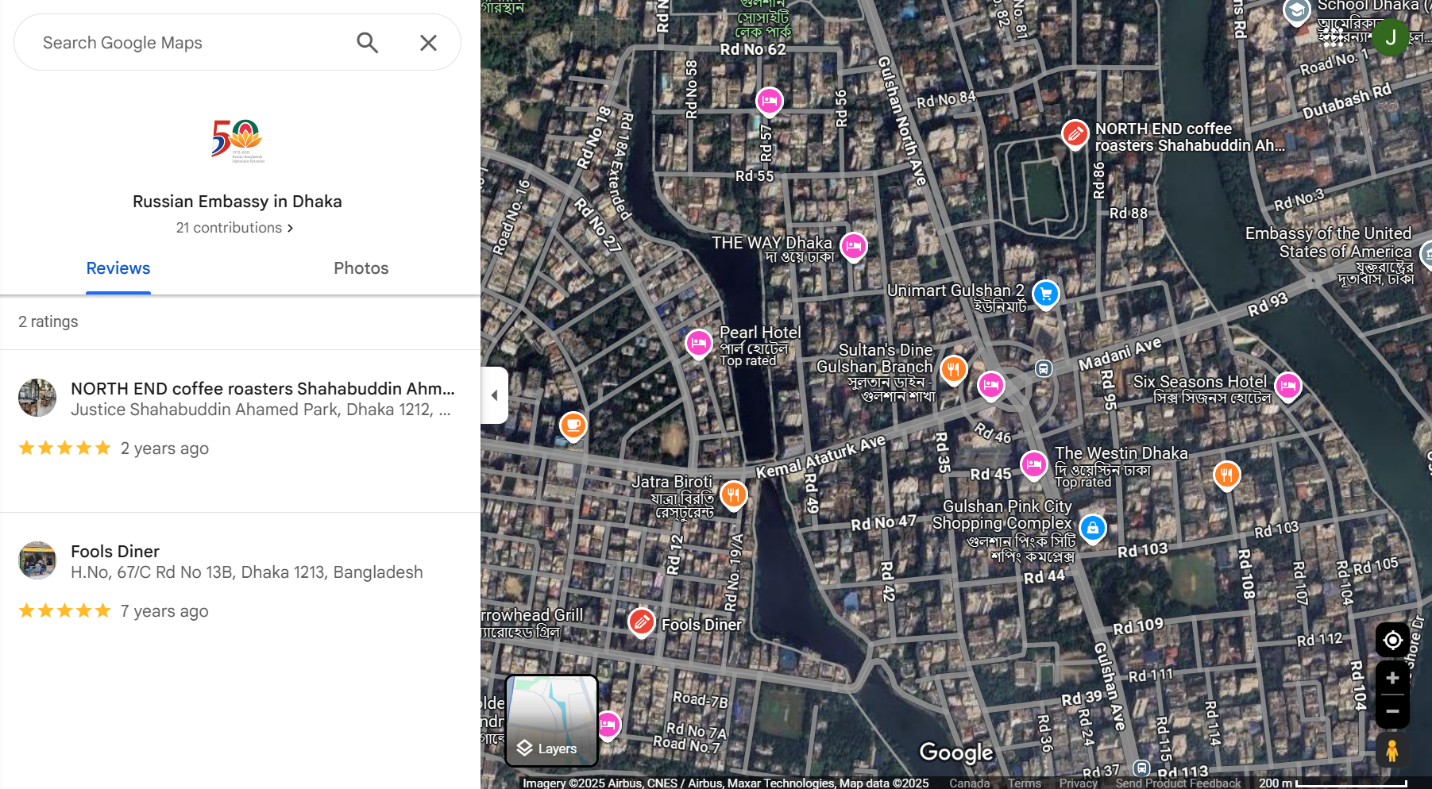
59 Russian embassy emails have Google accounts. According to Jordan’s research, only one of them has made the (inadvisable) decision to post reviews on Maps. The Russian embassy in Dhaka, Bangladesh gave two five star ratings: the Fools Diner at H.No, 67/C Rd No 13B, Dhaka 1213, Bangladesh on June 29, 2017, and North End Coffee Roasters at Justice Shahabuddin Ahamed Park, Dhaka 1212, Bangladesh on March 18, 2023.
We can only assume the service is worth compromising your safety for.
Jordan found no other embassy emails have posted reviews on Maps, but several have posted photos.
The Russian Embassy in South Africa (ruspospr@mweb.co[.]za) posted a photo of the building’s exterior in March 2012. Google Maps lists an “unknown place” as the photos’ location; the plaque visible in the photos makes clear that this is the Russian embassy.

The Russian Consul of Sri Lanka and Maldives (rusconsul.srilanka@gmail[.]com) posted two exterior photos in September 2024, featuring their door’s locking mechanism.
All these photo uploads remain up to this day for anybody to see. This is a major OSINT misstep. Altogether, the content posted by these email accounts on Maps makes embassy staff easier to profile, locations easier to confirm, and officials or employees easier to target for harm.

The Napster Anomaly: A Civilian in the Loop
Jordan found one anomaly that was truly bizarre. 317 Russian embassy and consulate email addresses are registered on Napster - more than Facebook, Google and Twitter combined.
This includes Washington, D.C., Zimbabwe, Jamaica, Bangladesh, Iran, Sri Lanka, UAE, Japan and India.
In the West, music streaming site Napster is as obsolete as flip phones or Blockbuster. OSINT Industries has confirmed this old-school music site isn’t widely popular in Russia either. Russians prefer to use homegrown alternatives like market leader Yandex Music (Яндекс Музыка), VK Music (ВКонтакте), or recently available Spotify – in fact, Napster has never been officially accessible in Russia, and ceased to stream music at all this January.
Even weirder, Jordan found at least 16 official embassy emails are directly linked to one Napster account: “Misterking”. The account bio reads "radiohead1234", and email address m*******king@gmail[.]com. Reverse searching the innocuous profile picture produced no results.
Via OSINT Industries, Jordan could link “Misterking” to:
- darconsul@gmail[.]com
- rusembzimbabwe@gmail[.]com
- rusconsjamaica@gmail[.]com
- rusafatt@gmail[.]com
- russconswdc@gmail[.]com
- rusembbd@gmail[.]com
- russianconsulgoa@gmail[.]com
- honycghydrusfed@gmail[.]com
- rus.consul.kolkata@gmail[.]com
- rusembiran@gmail[.]com
- pressservice.tokyo@gmail[.]com
- rusemb.srilanka@gmail[.]com
- russingtrade@gmail[.]com
- rusconsul.srilanka@gmail[.]com
- rusembuae@gmail[.]com
- ruvn.press@gmail[.]com

Who is ‘Misterking’?
An OSINT Industries search on m*******king@gmail[.]com produced hundreds of additional results too. Was this a burner account or something more concrete?
Name: M****** K***
Locations: Greater Seattle Area and Renton, Washington (based on Google, Yelp, LinkedIn, MyFitnessPal, Redfin, Peloton)
Activity period: Since at least 2010 (based on Chess.com account creation) - present (based on Google, Chess.com)
Registered on:
- Google (multiple devices across a decade)
- LinkedIn (public profile)
- Airbnb (with US phone number)
- Yelp (266 followers, extensive review history)
- Spotify
- Pandora
- Napster (obviously)
- Trello
- Dropbox
- PayPal
- Microsoft
- Other fitness, mapping, and social platforms
All this shows a long-standing personal digital footprint - it’s a real civilian account. At least 16 Russian embassy email addresses are linked to a single Napster account registered to a seemingly random US civilian.
OSINT Industries’ own investigations have been unable to locate a meaningful connection between M****** K*** and Russia. His children’s faces are clearly visible in his posted content; although his career in optical treatment is apolitical, one Google Review placed him at a taco stand just off DC’s National Mall.
To make things worse, this well-connected civilian’s credentials have appeared in over 20 major data breaches from 2008–2024.
Distiller
Alongside Napster, Jordan found another anomaly. 332 embassy addresses have profiles on Distiller, the liquor-reviewing app and “social network for whiskey lovers”. Why so many Russian embassy emails would be attached to a whiskey app is difficult to comprehend. Security risks aside, it’s surely not an endorsement of Russian vodka.
Jordan states “if I'd had more time I would've looked deeper into… hundreds of accounts that were detected on the Distiller website”. It’s possible that this anomaly links to the previous Napster activity, or further illuminates the choice to link with civilians like ‘Misterking’
This Was Not a Hack: A System That Fails Repeatedly
“The vast majority of the email addresses have been affected by data breaches…” – Jordan, an OSINT and SOCMINT Analyst [Source: OSINT Industries]
The most startling element of Jordan’s report is the sheer quantity of data breaches Russian embassy emails have been subject to. Jordan highlighted the “February 2019 Verifications.io breach and March 2022 Vladolf Putler paste” as major sources.
Over 190 distinct Russian diplomatic email addresses have been breached, from 90 countries and territories, from 2011 to 2025.
Email OSINT mistakes - reusing credentials, using consumer providers, publicising credentials - caused these breaches, not sophisticated attacks or hacking attempts. Consumer email accounts are over 4x more likely to appear repeatedly in breach datasets than official domains, making the causes crystal clear in Jordan’s data. 61% of emails breached are mail[.]ru, yandex[.]ru, gmail[.]com, hotmail[.]com, yahoo[.]com addresses.
Only numbers can address the scale and scope of these failures. Statistically speaking:
- 100% of the 324 addresses appear in at least one breach dataset.
- Roughly 80% of Russian embassy emails appear in two or more breaches, indicating credential reuse.
- Roughly 50% appear in five or more separate breach events, indicating persistent credential reuse after breach has occurred.
- Roughly 10% appear in ten or more breaches, indicating chronic credential reuse - likely after notification of a breach.
The most common breach types are mail verification and enrichment datasets (e.g. Verifications.io, Covve, Data Enrichment Exposure), affecting 75–80% of addresses. Spam botnets or combo lists made up 60–65%; major platform breaches (i.e. Adobe, LinkedIn, Twitter, Canva, Bitly, Nitro, etc) made up 20-25%; the highest-risk credential-stealer logs (i.e. RedLine, ALIEN TXTBASE, stealer dumps) made up 35-40%.
A shocking (or satisfying) 55-60% of breaches came from politically motivated leak collections, like ‘Vladolf Putler’.
Geographically, many exposed accounts cover conflict zones, sanctions-heavy environments or intelligence-contested regions. The Americas represent 7% of those breached, 21% come from Asia and the Pacific, and 34% come from Europe. Africa and the Middle East, some of Russia’s most volatile interests, dominate with 38% of breached credentials.
Addresses with breached credentials include embassies and consulates, postings in NATO and EU states, and the by-now usual email suspects in military, naval, and defence attaché offices like Washington, D.C.
From a temporal angle, historic failure isn’t just historic. The earliest breach came in 2011, with the peak exposure period during the email (in)security golden age of 2017-20. A second spike came in 2022, driven by Ukraine-related dump collections. Stealer logs and Telegram combo lists continue through 2024–2025 – so current criminal ecosystems have access to embassy-linked credentials, as well as political opponents.
Risk-taking email behavior from Russian embassies is not a bug, it’s a feature. These breaches are the result.
Predictable Outcomes: How OSINT Cuts Both Ways
Jordan’s findings point to Russian diplomatic and military email infrastructure as sloppy, over-exposed, and repeatedly compromised. If your diplomatic email system runs on Gmail, reaching the credentials of the world’s most dangerous superpower doesn’t take elite adversaries burning zero-days. Compromises are the natural and predictable outcome of Russian diplomats’ own OpSec and OSINT mistakes.

Today, they’re breached. Tomorrow, Russian embassy officials could be facing long-term surveillance or infiltration, or impersonation of diplomats and military officials. Internal compromises like credential-stuffing and SIM-swap attacks are painful for an individual, but the stakes are so much higher here. Even a simple social engineering attempt could have devastating geopolitical ramifications. The illegal war in Ukraine has led to the closure of countless Russian consulates and embassies, and considering their security measures, this may be doubly wise.
The Russians’ consumer emails, credential reuse, public platform registrations, and careless behavior are mistakes, but they’re also intelligence opportunities - for adversaries, but also for the right investigator. An attack surface is also an OSINT gateway. In good hands, Jordan’s work with OSINT Industries is only the beginning.
It’s also worth stating that Jordan’s incredible work would have been impossible without our platform.
“Russia, Russia, Russia”... Donald Trump’s words here intended to express that sustained Russian interference efforts in the US were a fraud; a hoax that proved to be anything but. With simple OSINT Industries searches, Jordan proved Russia’s own institutions suffer from the very email weaknesses they have weaponised abroad.
"Russia, if you're listening, I hope you're able to find the 30,000 emails that are missing… I've got to be honest with you, I'd love to see them." – U.S. President Donald Trump on email hacking. [Source: BBC]
To find out more about Jordan’s work, visit:
Jordan’s LinkedIn
See Jordan’s previous work with OSINT Industries in another Case Study.
“In a transgressive YouTube culture where male-on-male sexual assault is often reduced to a punchline, this OSINT investigation clearly demarcates where the culture should change, and the laughter should end…”
Read more: Comedy to Crime Scene: Calling Out a Youtube Sexual Assaulter With OSINT
Start your free enterprise trial
Get Free TrialReveal what's behind any contact, instantly.
We want to hear your story!
Inspire Others
Educate about what OSINT can do.
Positive Publicity
Share your success with the world.
Support #OSINT4Good
Be part of the OSINT story.


.avif)